designing a defense-in-depth architecture for online election security
a cybersecurity capstone project
nicole mullen
12/12/20253 min read


project scope
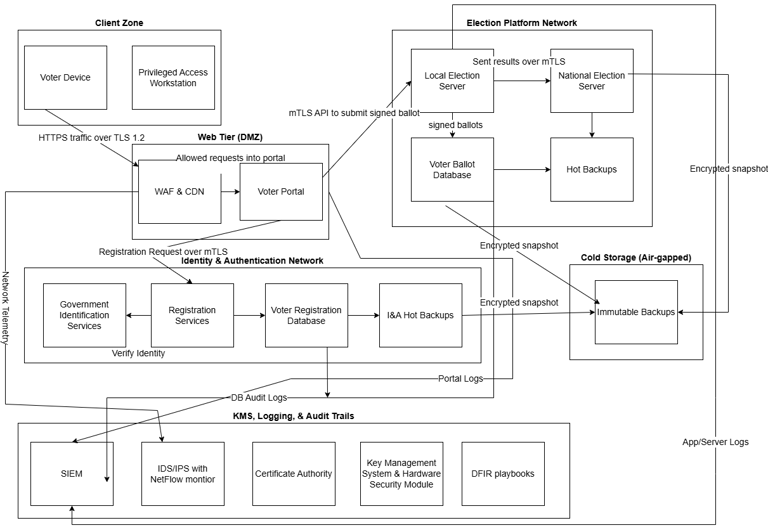
For my cybersecurity capstone, I worked on a team project focused on designing a secure architecture for a fully online national election system. The goal was to create a defense-in-depth model that could support voter authentication, ballot protection, secure transmission, monitoring, and recovery while reducing single points of failure. Our final design used a decentralized approach with local and national election servers, segmented trust zones, layered authentication, encrypted ballot handling, and strong logging and backup strategies.
the core idea
At the heart of the project was a simple principle: a secure online election platform cannot rely on one control. It has to rely on many controls working together.
We designed the environment with separate zones for the client side, the public-facing web tier, identity and authentication services, the election platform itself, cold storage, and security operations. That separation was intentional. Public-facing services should not sit directly beside sensitive ballot storage. Identity verification should not be tightly coupled with the system that stores ballots. Administrative systems should be restricted, monitored, and isolated. This kind of segmentation helps reduce the blast radius if any one component is compromised.
protecting voter identity without exposing the ballot
One of the most interesting parts of this project was balancing identity verification with voter anonymity.
A trustworthy election system needs to confirm that each voter is eligible and only votes once. At the same time, it cannot create a direct link between a person’s identity and their ballot. Our design addressed that by separating identity proofing from ballot casting. After successful authentication, the system would issue a one-time anonymous token so the voter could cast an encrypted ballot without exposing personal identity data during the voting transaction itself.
We also incorporated layered voter authentication through MFA, digital credentials, and mutual TLS between systems. Internal services would authenticate one another using short-lived certificates issued by an internal certificate authority, with key material protected through key management infrastructure. This approach helped support both strong access control and stronger resistance to impersonation or man-in-the-middle attacks.
the biggest takeaway
monitoring, detection, and threat response
securing ballots in transit and at rest
Protecting the ballot itself was another major focus.
In our proposed model, ballots are encrypted on the voter’s device before transmission, sent over protected channels, and handled through authenticated system-to-system communication. We also explored the role of end-to-end verifiability and homomorphic tallying to support confidence in the final vote count without exposing individual selections. That matters because election security is not just about blocking attackers. It is also about preserving confidence that votes were received, stored, and counted without tampering.
Within the election infrastructure, we paired encryption with integrity protections, append-only logging, and controlled storage workflows. Ballot databases were designed with least privilege in mind, along with audit trails, separation of duties, and backup paths for both operational recovery and disaster scenarios. Hot backups supported continuity, while immutable cold storage snapshots supported resilience against catastrophic events such as ransomware.
Because elections are high-value targets, we also treated monitoring as a first-class requirement rather than an afterthought.
Our design included centralized logging into a SIEM, supported by IDS/IPS, network telemetry, and key usage monitoring. We identified a range of alert conditions that should trigger investigation, including repeated failed logins, unexpected administrator privilege changes, ballot discrepancies, traffic spikes consistent with DDoS activity, and suspicious cryptographic key operations. We also tied this into incident response planning, because visibility alone is not useful unless there is a process for containment, investigation, and recovery.
This part of the project reinforced something I care about as I grow in cybersecurity: security architecture is only as strong as the operational discipline behind it. Good design has to be supported by monitoring, logging, playbooks, and people who know how to respond under pressure.
The biggest lesson from this capstone was that online election security is not a problem with a quick fix.
There is no single product, platform, or cryptographic feature that suddenly makes internet voting safe. The challenge is architectural. It requires layered controls, privacy-by-design thinking, strong governance, secure key management, careful segmentation, backup planning, and constant monitoring. Even then, the path to a trustworthy nationwide implementation would take significant time, standardization, testing, and funding. Our research suggested that jurisdictions could make meaningful progress in the near term through stronger encryption, MFA, DMZ architecture, and better logging, but a truly unified and trustworthy large-scale online election platform remains a long-term challenge.
why this project mattered to me
This capstone gave me the chance to apply cybersecurity concepts in a way that felt realistic, technical, and mission-driven. It brought together network security, access control, secure architecture, logging, resilience planning, and policy considerations in one project. More than anything, it challenged me to think about how security decisions affect trust, not just systems.
That is one of the reasons this project stands out to me. In election security, the goal is not only to protect data. It is to protect confidence in the process itself.